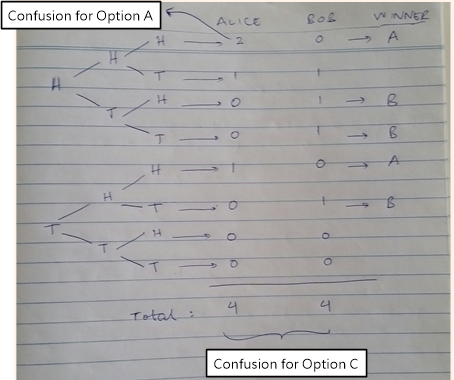
The Monty Hall problem is an interesting puzzle loosely based on an American TV game show Let’s Make a Deal hosted by Monty Hall. While the puzzle looked simple, it perplexed some of the brightest mathematical minds in the United States, including the great Paul Erdös who was one of the most prolific mathematicians of the 20th century. This continues to be the case today. I looked upon a number of references to find the source of confusion in the Monty Hall problem but failed. All I found was different solutions. Therefore, I built one myself with the usual from
Continue reading