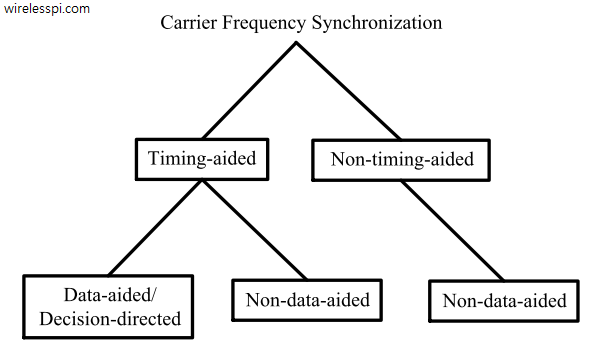
We have discussed before that carrier phase synchronization is done at the end of the Rx signal processing chain due to the very nature of the DSP implementation. And that almost all DSP based phase synchronization algorithms are timing-aided. Timing acquisition implies knowing the symbol boundaries in the Rx sampled waveform which is equivalent to identifying the optimal sampling instants where the eye opening is maximum and Inter-Symbol Interference (ISI) from the neighbouring symbols is zero. In the case of Carrier Frequency Synchronization (CFO), this is not true. From a previous post on the effect of CFO, we know that
Continue reading